Menu Navigation
Security Maintenance ... Security Groups
About Groups
Groups are used to define common application resource accesses for a set of users. This way, you can predefine the levels of access for various employee functions and then assign those functions to users, so that they have appropriate access. This method is of assigning access should be used by most companies, and is especially useful for companies with heavy employee turnover. A number of user groups have been provided for your convenience. Feel free to use these groups, or create your own as necessary.
In this Topic
Field by Field Help - Group List
Field by Field Help - Update Groups screen
Q & A - Groups
Related Topics
15.1 Security Setup
15.2 Users
Field by Field Help - Group List
Add A Security Group
Click this button to create a new security group record.
Update Security Group
Click this button to modify the highlighted security group.
Delete Group
Click this button to delete the highlighted security group .
Group Application Access
Click this button to view the applications and this user's status with those applications.
Group Users
Click this button to view the users that do and do not belong to this group.
Copy Access From One Group to Another Group
Click this button to copy the accesses of one group to another. Especially useful when you have several groups with similar security access.
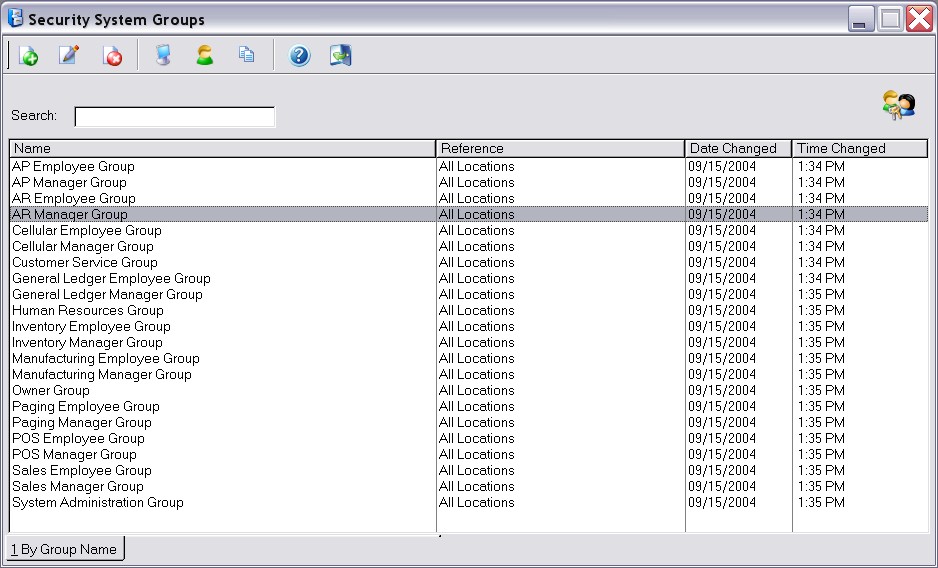
Figure 14-3. Group List screen
Field by Field Help - Update Groups screen
Group No.
Displays the auto-generated number for this group record.
Name
Enter a new name for this security group.
Location
Enter the specific location for this group or ALL if you do not want the group to be limited to a specific location.
Group
Defines the permanence of this group. Select Group for Permanent and Temporary for a temporary security group.
Expire Date
If temporary, select the date that this group's login abilities should expire.
Q & A - Groups
| Q01. | Can an individual user be part of more than one group?
|
| A01. | Yes. Users can belong to as many groups as is available in Security Administrator. The user will then be given access to the total resources that all of the groups they have joined have. For example, if group A has access to resources 1 and 2, and group B has access to resources 1, 3, and 4, then an individual belonging to both groups will have access to resources 1, 2, 3, and 4.
|
|
|
| Q02. | What if a change needs to be made to one user's security profile in the group?
|
| A02. | If that user needs more resources opened to them in the program, those resources can be added to the user's individual security profile. If the user needs resources removed from their profile, a new group and or individual profile will need to be made for that user as the security in the program is additive only. In other words, the total security on an individual user's profile is the result of the adding of the user's security profile and the group security profile to which that user belongs.
|
|
|
| Q03. | Why would our company need temporary groups?
|
| A03. | Temporary groups are good for temp employees, auditors, or other people who would need access to the program, but only for a limited amount of time.
|
|
|
| A04. | Visit our website's Technical Support section.
|